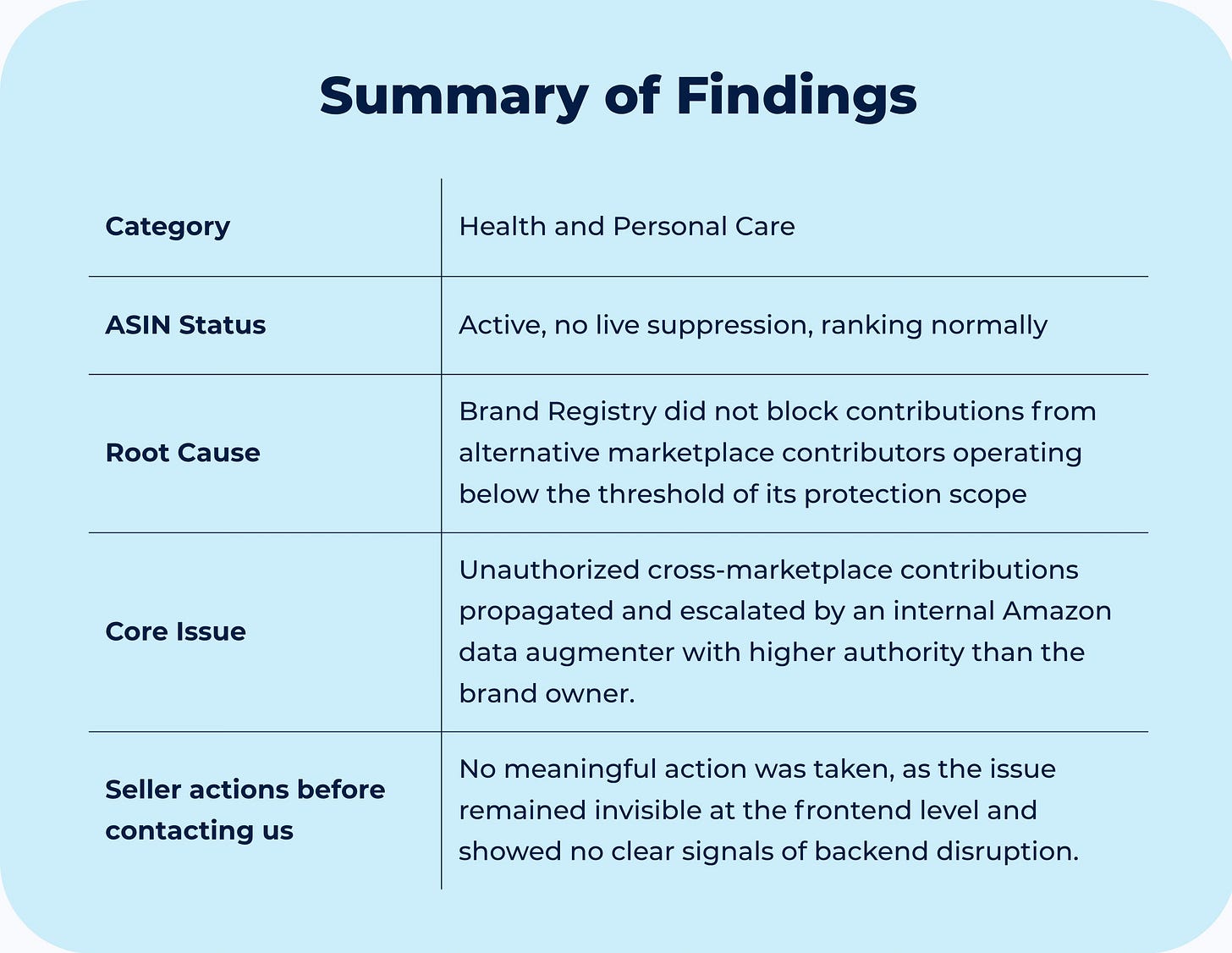
Case #019 - 🥴 Amazon translated a competitor's attack into 4 languages. Automatically.
A third-party seller pushed backend attributes, and an Amazon data augmenter amplified them across languages, overriding the brand owner despite Brand Registry.
If you’re new here, welcome.
If you’ve been reading for a while, thank you for being here.
Each week, we break down one real Amazon case from the field. Not to share tactics, but to decode how Amazon’s system actually behaves and what to do when it breaks.
All past cases live in a single searchable archive, built to help you identify recurring patterns across time.
Context
The Brand Registry assumption
The seller had an ASIN listed under Health and Beauty, this ASIN was part of a variation family of approximately 300 child ASINs, and for the record, the brand was enrolled in Brand Registry.
At some point, a third-party seller began pushing contributions into the backend of the listing, injecting content into attribute fields with no relation to the actual product. By the time the issue was identified, approximately 70 unwanted attribute contributions had accumulated in the backend across multiple fields.
The initial assumption was straightforward: Brand Registry provides catalog authority. If you are the brand owner and your contributions have a higher rating than any third-party contributions, the system protects the listing from unauthorized edits.
The seller had no indication that contributions were accumulating in the backend, the detail page appeared intact, the ASIN was active, ranking at position 12 within its variation family, and generating sales.
Diagnostic
How the system handles version transitions
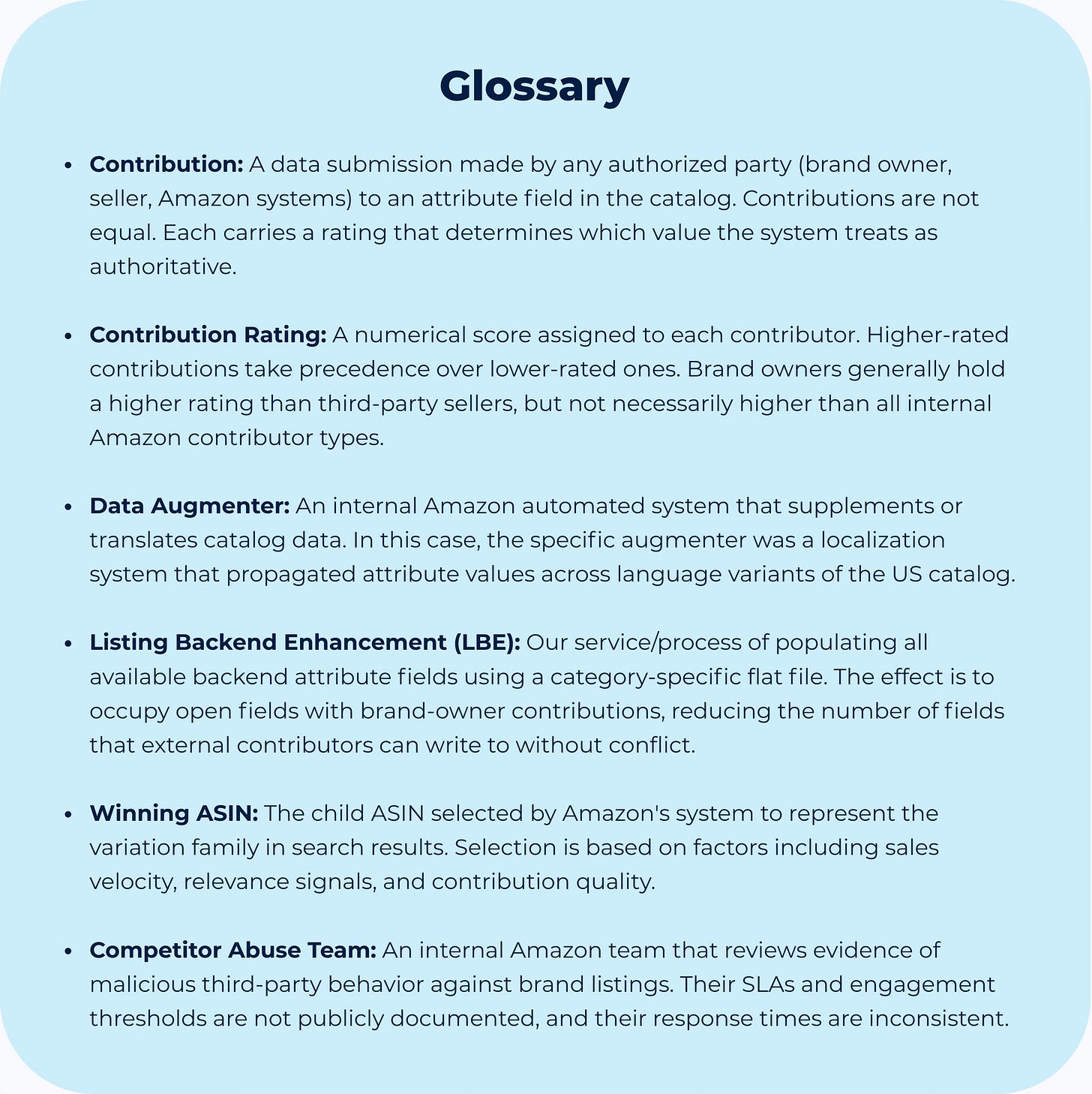
The unusual aspect is that the attack did not originate in the US marketplace. A third-party seller submitted contributions from the Mexico marketplace through a flat file. Amazon’s catalog system recognizes the product as the same unit across marketplaces and treats the contributions as valid input to the shared attribute store.
What’s interesting is that the seller’s contributions carried a rating of approximately 30, which is below the brand owner’s contribution rating, and therefore addressable through a standard flat file submission.
This is the first layer of the problem: the catalog does not validate whether a contributor has authorization in the destination marketplace, it validates whether the contribution is structurally eligible to propagate.
The second layer is where the attack is compounded.
Because Amazon operates internal contributor types called data augmenters (automated systems that perform tasks such as translating content across language versions of a marketplace and/or adding “relevant data to listings). One of these augmenters, identified in the backend as “data-augmenter-asin-localization-mozart-us,” detected the Mexico-origin contributions and distributed them across 4 language variants of the US marketplace:
Arabic
Spanish
German
Portuguese
The contributions had already been written in multiple languages by the external seller, and the augmenter treated them as eligible catalog content and propagated each version to its corresponding language variant. The system performed its function correctly, it distributed the content it was given, but the content happened to be attribute-spam designed to trigger compliance flags, and that is what the augmenter amplified at scale.
The critical distinction is this: rated at approximately 50 to 60, the data augmenter’s contributions sit above both the third-party seller and the brand owner in the catalog authority hierarchy. Once the augmenter wrote those values to the attribute store, they could not be overwritten by a flat file submission from the seller account.
The seller’s contributions, even as Brand Registry owner, do not outrank an internal Amazon contributor type. Brand Registry provides authority over human contributions from external sellers, but it does not grant authority over Amazon’s internal contributors. These are separate layers of the catalog hierarchy, and they operate under different permission structures.
Of course the UI showed nothing like an error, but the backend held approximately 70 attributes containing content such as adult product terms, pesticide-related language, and sanctioned-origin product references.
These values had been added into fields with no relevance to the product like brake style, lens color, fabric type, scent, and furniture finish. The intent was to trigger an automated compliance review and either suppress the listing or force a policy violation.
If this feels familiar or something similar is happening in your catalog, you’re not the only one. we’ve seen how these situations unfold and we’re here if you need a second set of eyes.
Though Process
How the decision was made
The first seller’s instinct in a case like this is to escalate directly with Seller Support and request removal of the fraudulent contributions. That path was evaluated and deprioritized for a specific reason: Seller Support does not have access to the SKU attribute remover for data augmenter contributions.
So, escalating would create a support case with no actionable resolution path for the highest-rated contributions.
The second instinct is to file a brand violation report through Brand Registry, but Brand Registry violations are scoped to external sellers making unauthorized edits, and the data augmenter is not an external seller. It is an internal Amazon system, which means the violation report routes to a team with no jurisdiction over that contributor type. The case would move, but nothing would change.
The correct evaluation required separating contributions by source and rating before selecting any action.
Contributions from the third-party seller, rated at approximately 30, were below the brand owner’s contribution rating, making them addressable through a flat file submission that populated every relevant attribute field with brand-controlled data, reducing the seller’s contributions to a lower-priority state in the attribute store.
Contributions from the data augmenter, rated at approximately 50 to 60, were above the brand owner’s contribution rating, so these required direct deletion from the backend through Catalog Support escalation.
The localized propagations required a separate line of work. Each of the 4 language variants held its own discrete contribution record in the backend, so each one had to be identified and removed individually by tracing back to the originating augmenter session.
Evaluating what the system can and cannot respond to before acting is what separates a resolved case from one that generates activity without outcomes.